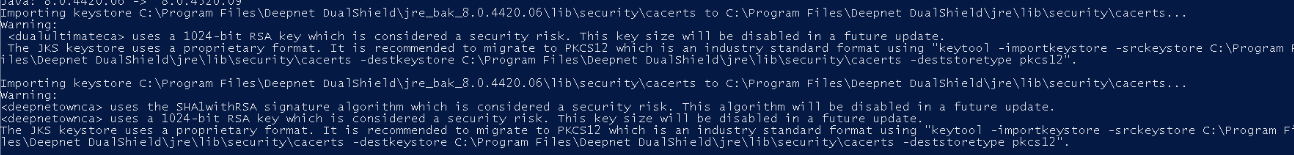
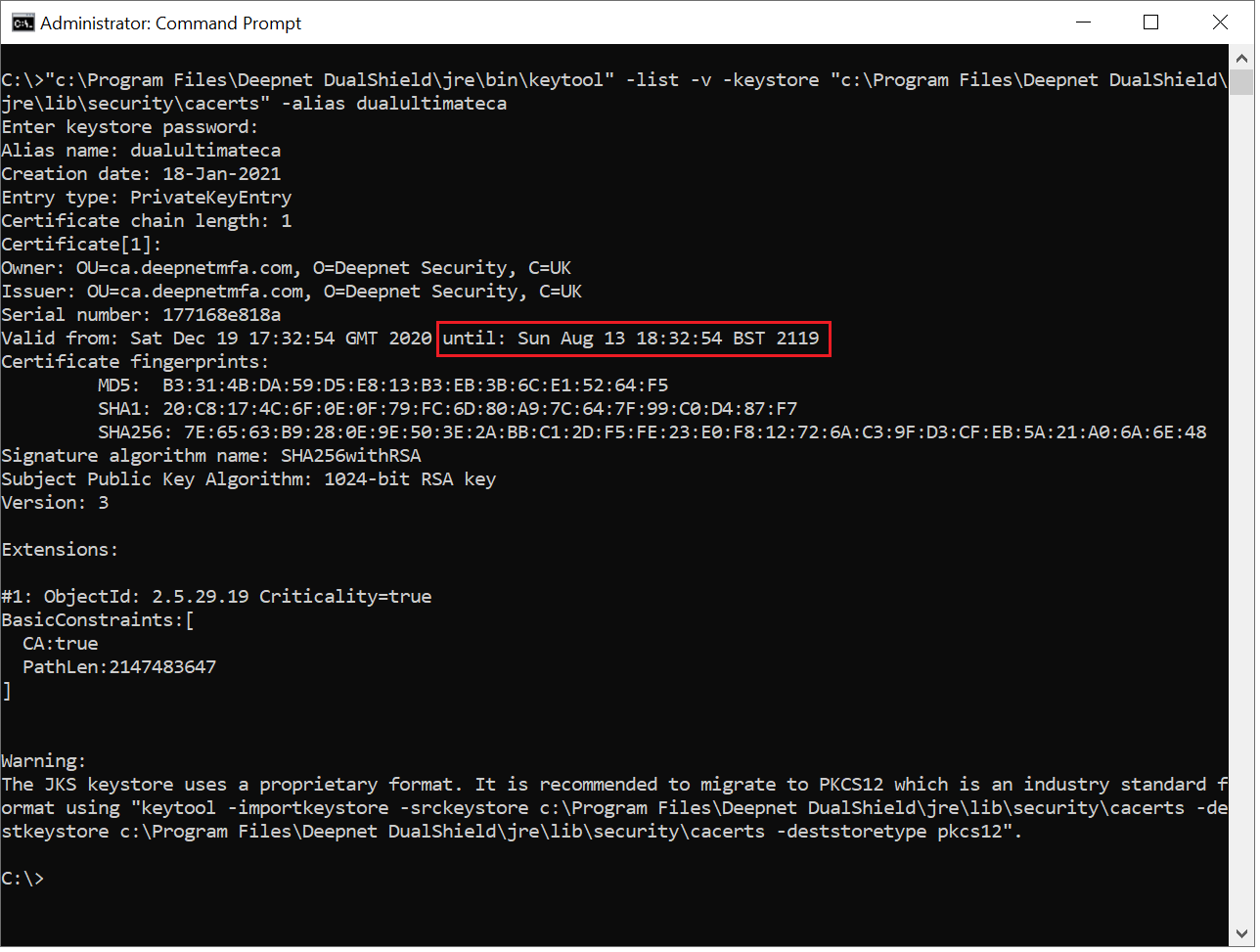
During installation we package in our own root CA plus internal Agent and IDP certificates. Some of our long-term customers may see this warning when updating the DualShield Framework
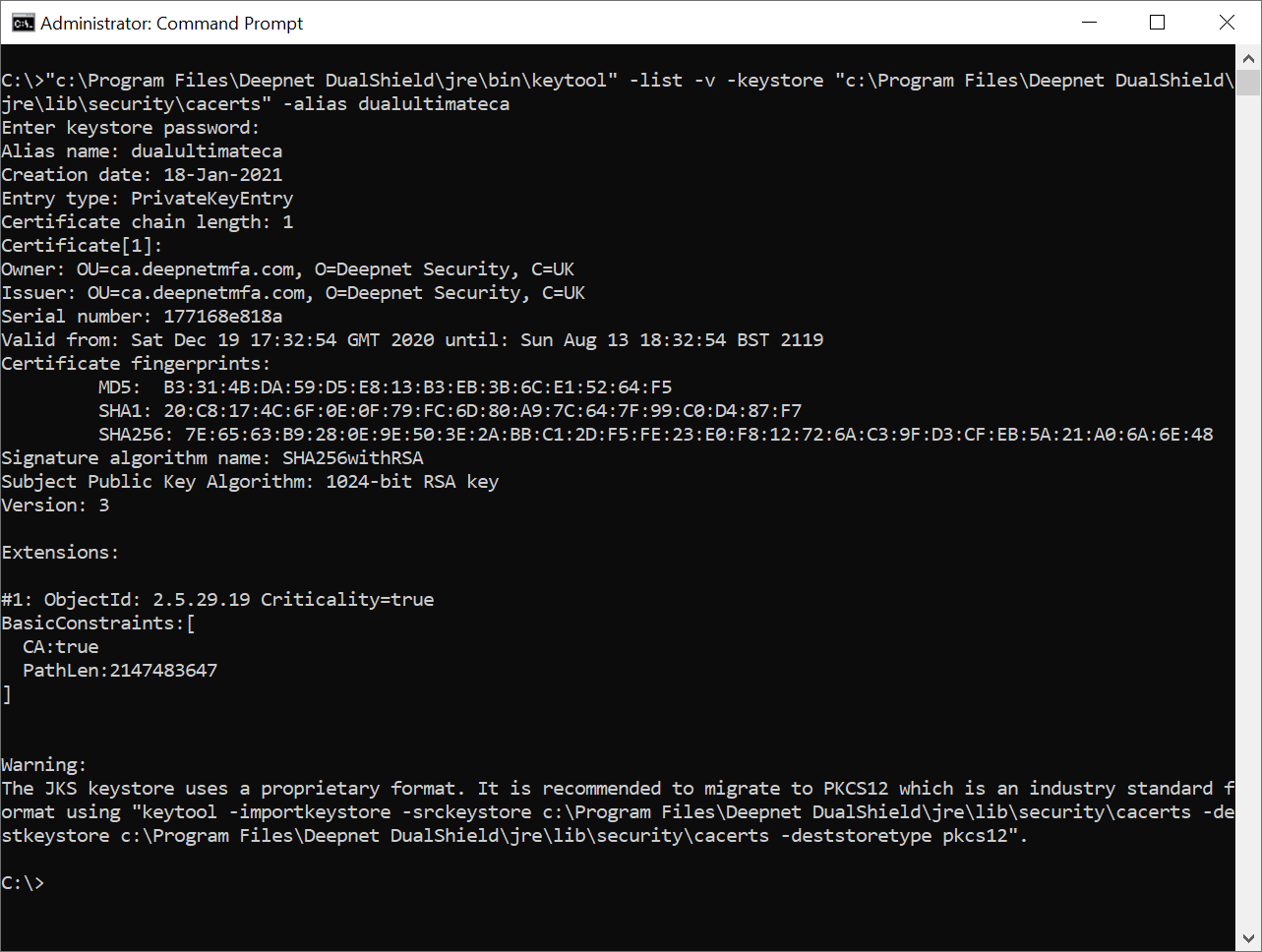
This is because the RSA key used in the installation of their original older version of DualShield Authentication Server would have been 1024 bit, which was acceptable at the time.
It is now recommended to update this key to 2048 Bits. There are quite a few steps to this process. All the instructions in this guide should be followed precisely.
Upgrade DualShield
Upgrade to DualShield 7.3.0 or later version, 7.3.4 is recommended.
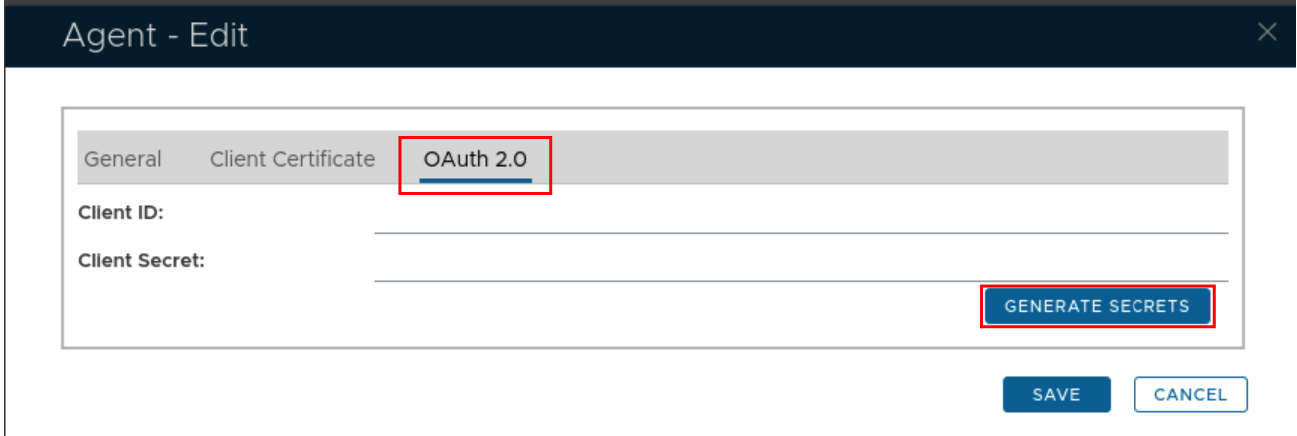
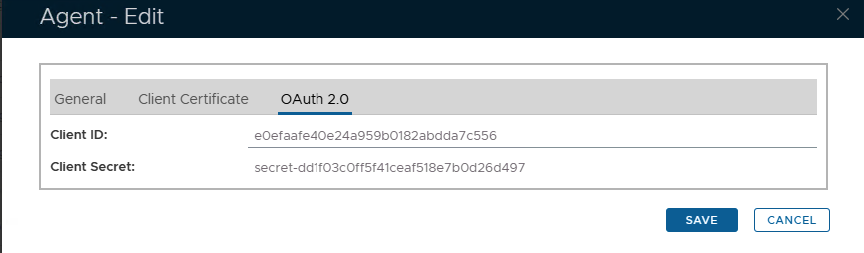
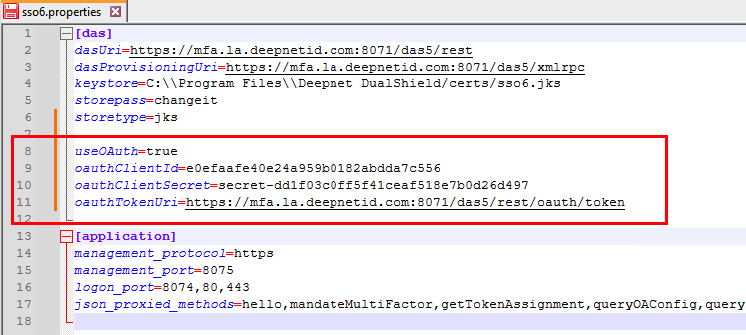
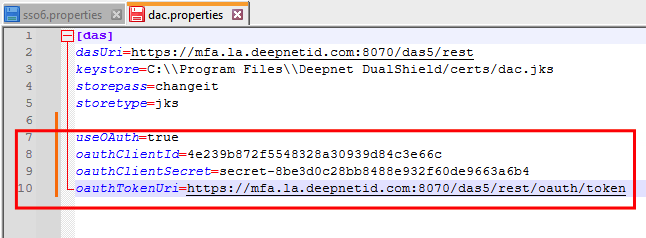
Setup OAuth Agent Authentication
Regenerate the root CA
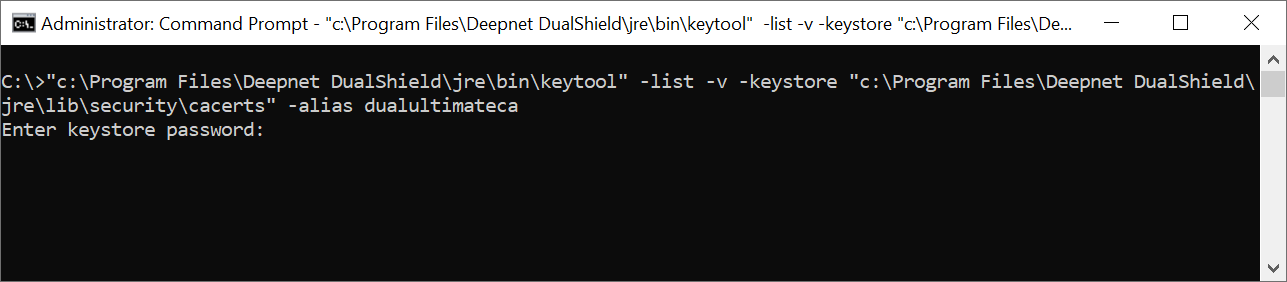
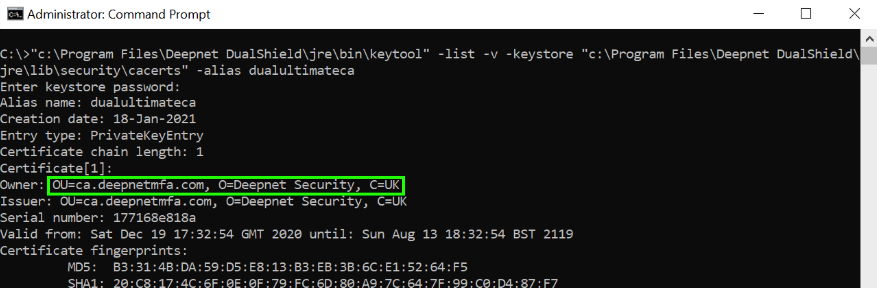
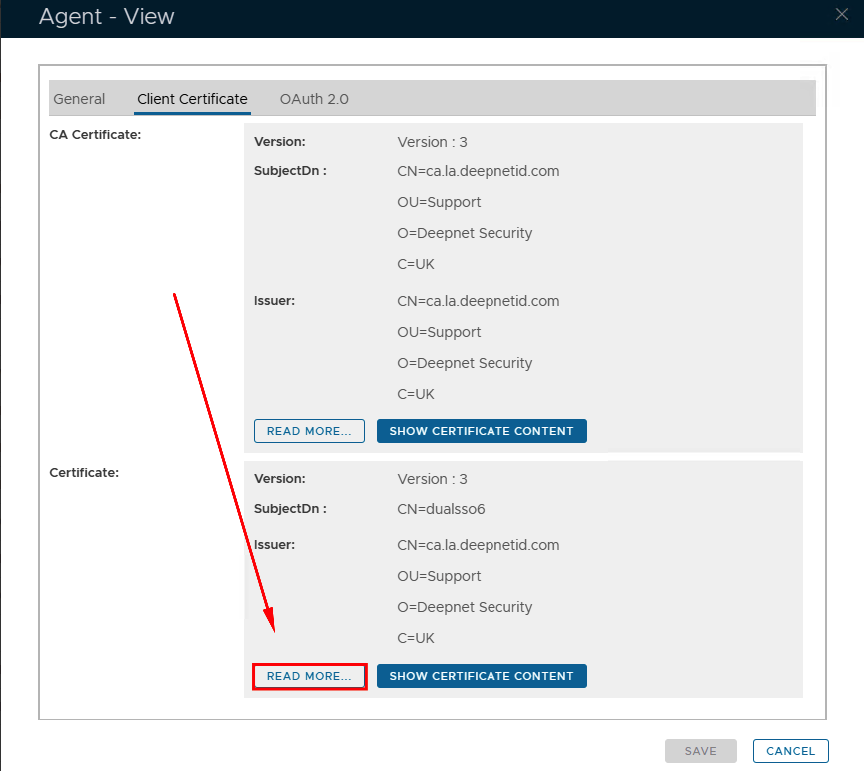
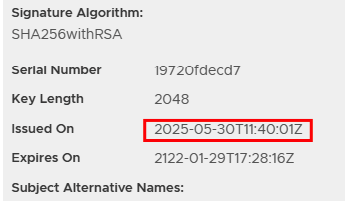
...However, instead of checking for the date, you will be checking for the owner...
2) Note down the owner details. In this example, it is: OU=ca.deepnetmfa.com, O=Deepnet Security, C=UK
3) Backup the current cacerts file:
Run Command Prompt in admin mode and run the following commands:
cd C:\Program Files\Deepnet DualShield\jre
copy "lib\security\cacerts" "lib\security\cacerts.backup"
4) Delete the old root CA:
bin\keytool -delete -alias dualultimateca -keystore lib\security\cacerts -storepass changeit
5) Generate a new root CA with a keysize of 2048, using the owner information you acquired in step 2:
bin\keytool -genkeypair -alias dualultimateca -keyalg RSA -keysize 2048 -validity 36500 -dname "OU=ca.deepnetmfa.com, O=Deepnet Security, C=UK" -ext bc=ca:true -keystore lib\security\cacerts -storepass changeit -keypass changeit
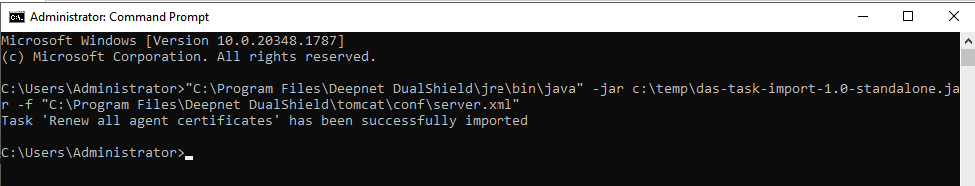
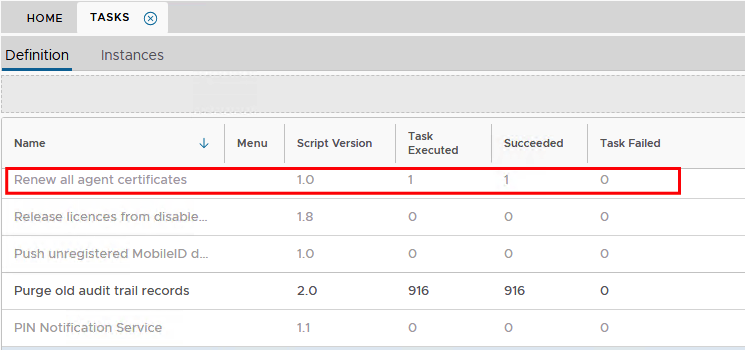
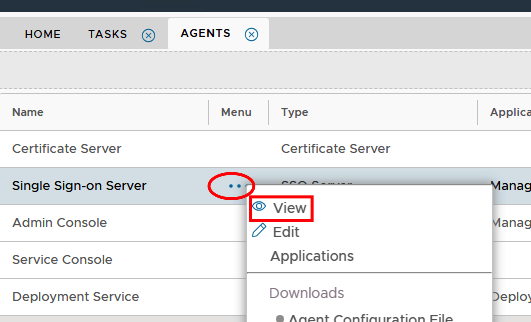
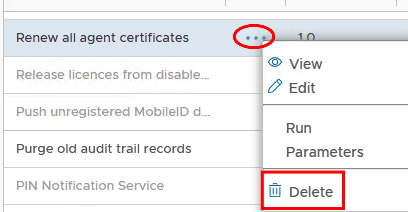
Regenerate all agents and idp certificates
Method 1
Method 2
SAML Integrations
IMPORTANT IF YOU HAVE A SAML INTEGRATION!
After completion of the above steps, you MUST provide the third party Service Provider with the updated IDP Metadata/Certficate.
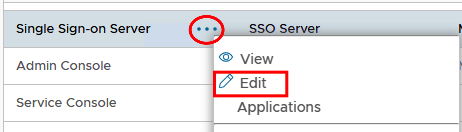
Go to SSO> SSO Servers, click on the corresponding ellipsis and select the files you need to download from the menu..