In some circumstances, such as in the initial stage of deploying MFA across your entire domain and user base, you might not want to enforce MFA on all user accounts, on the first day. Instead, you might consider enforcing MFA gradually across your user base, in stages. To do so, you can create a special user group in AD and a couple of logon policies in DualShield. For the simplicity of this guide, let's call this AD group as DualShield 2FA group. The strategy is that on some individual users or a user group only.
In this guide, we will describe how to configure your DualShield system so that MFA is only enforced on a user group called "DualShield 2FA". In other words, MFA will only be enforced on users who are a member of the DualShield 2FA group. All other domain users will be able to continue to login into the domain with a password only.
First, you will need to create a user group called DualShield 2FA in your AD server.
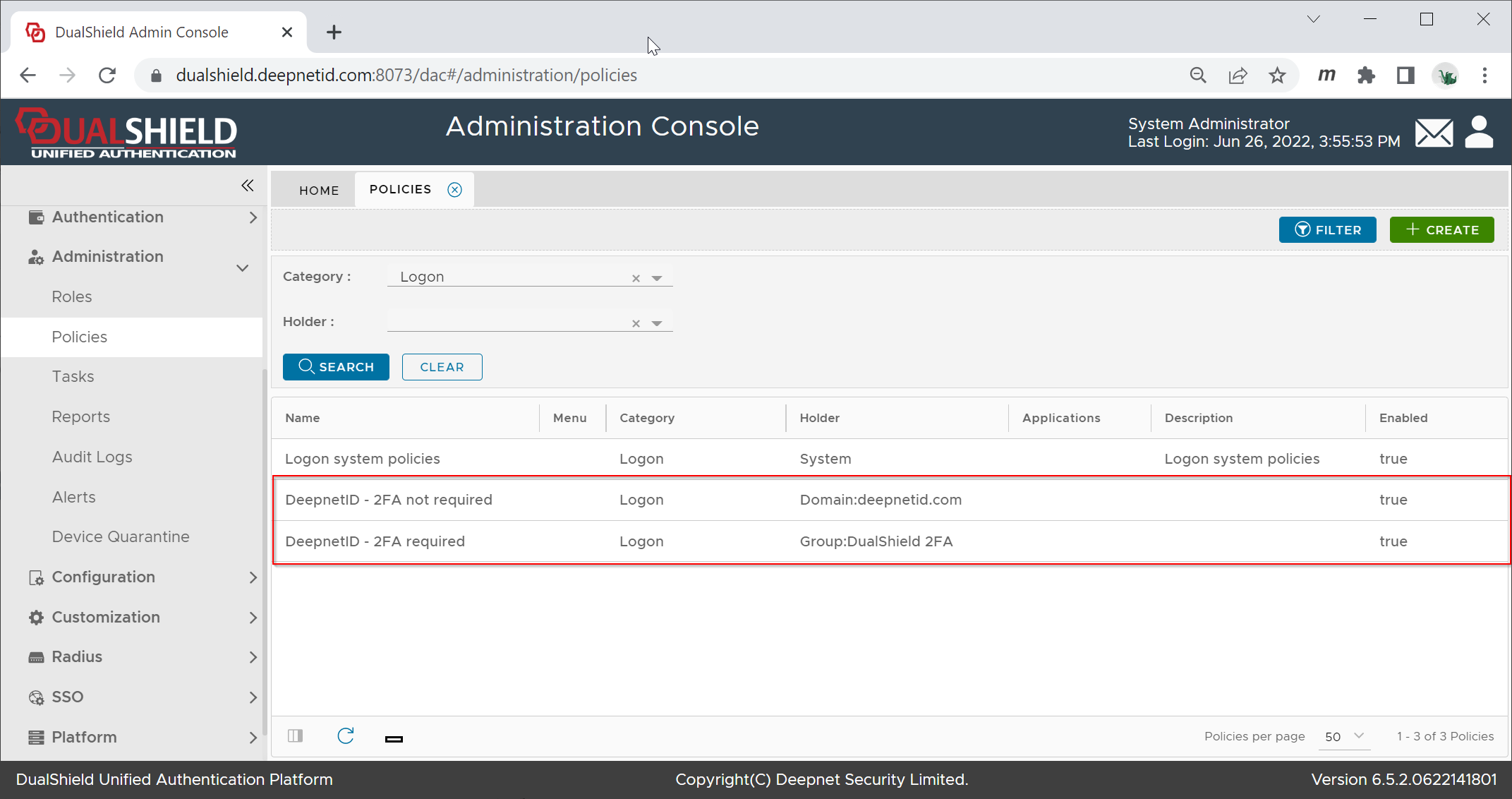
Then, you You will create 2 logon policies in your DualShield server. A , a domain policy and a group policy.
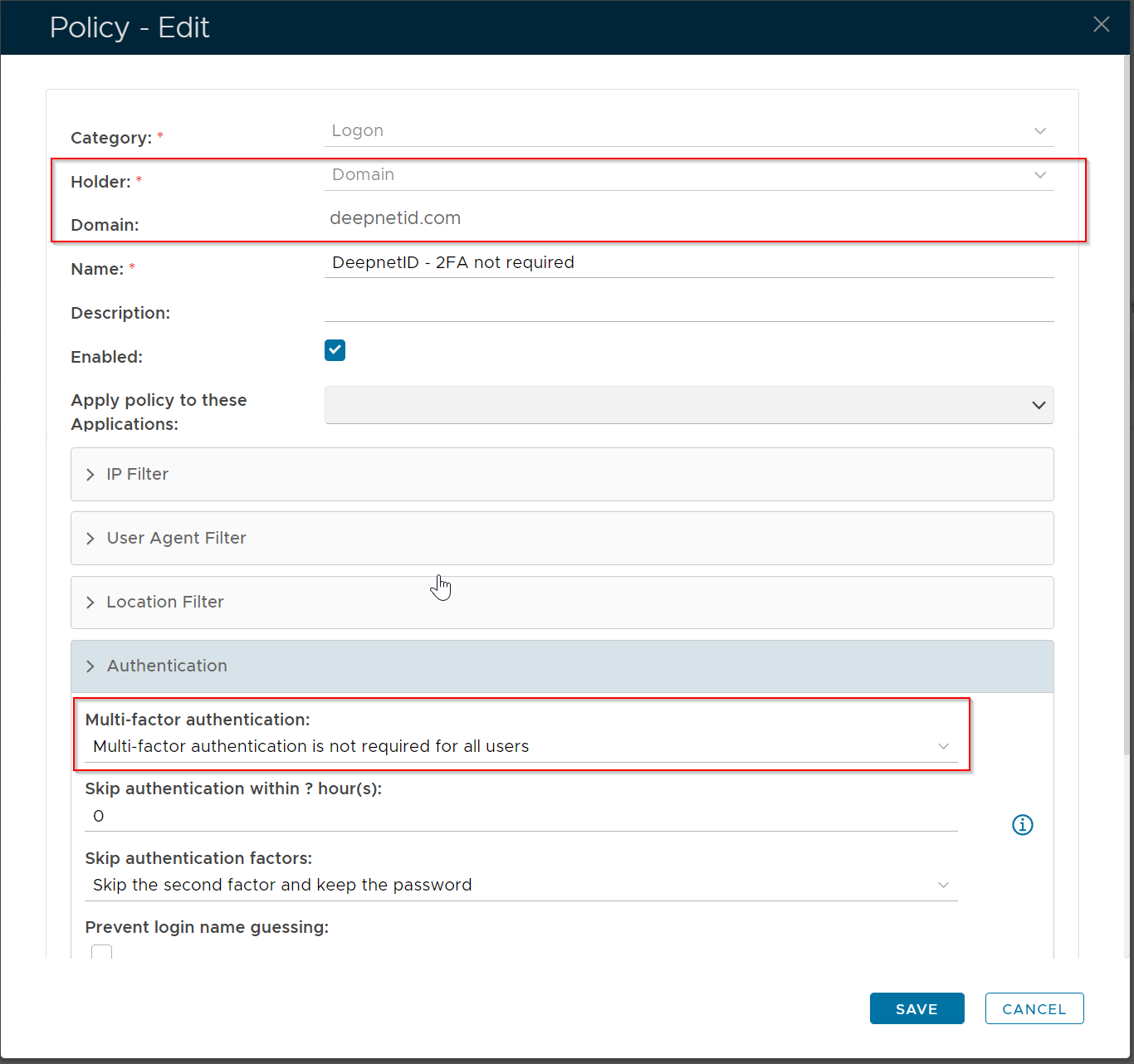
The domain policy is bound to the entire domain, and multi-factor authentication is not required on all users.
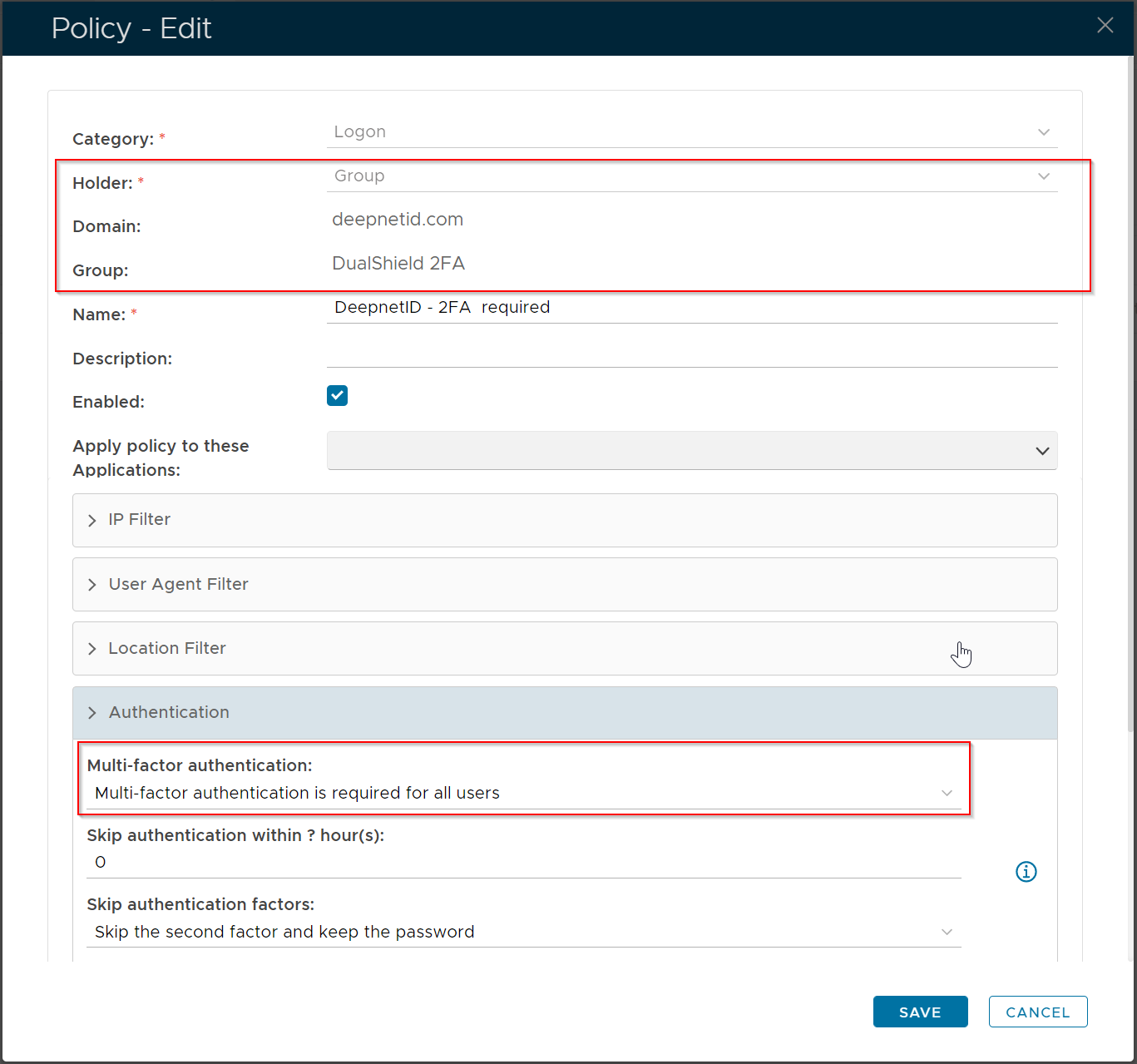
The group policy is bound to the DualShield 2FA user group, and multi-factor authentication is required on all users.
Below is an example.
Domain Logon Policy
| Section | |||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
Group Logon Policy
| Section | |||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
...