By default, the DualShield installer creates a default system administrator user called "sa". This is an internal user account managed by the DualShield server itself. You can create more internal user accounts for your admin or helpdesk team members who will be allowed to access the Admin Console, or you can allow your AD users to access the Admin Console.
To allow AD users to access the Admin Console, follow the steps below.
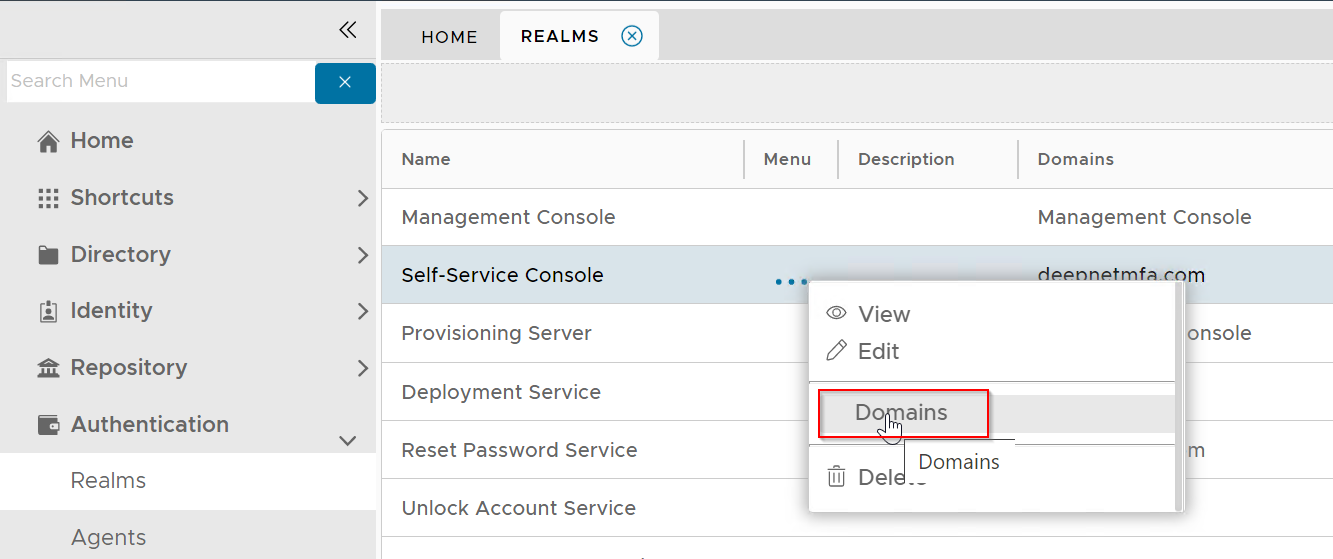
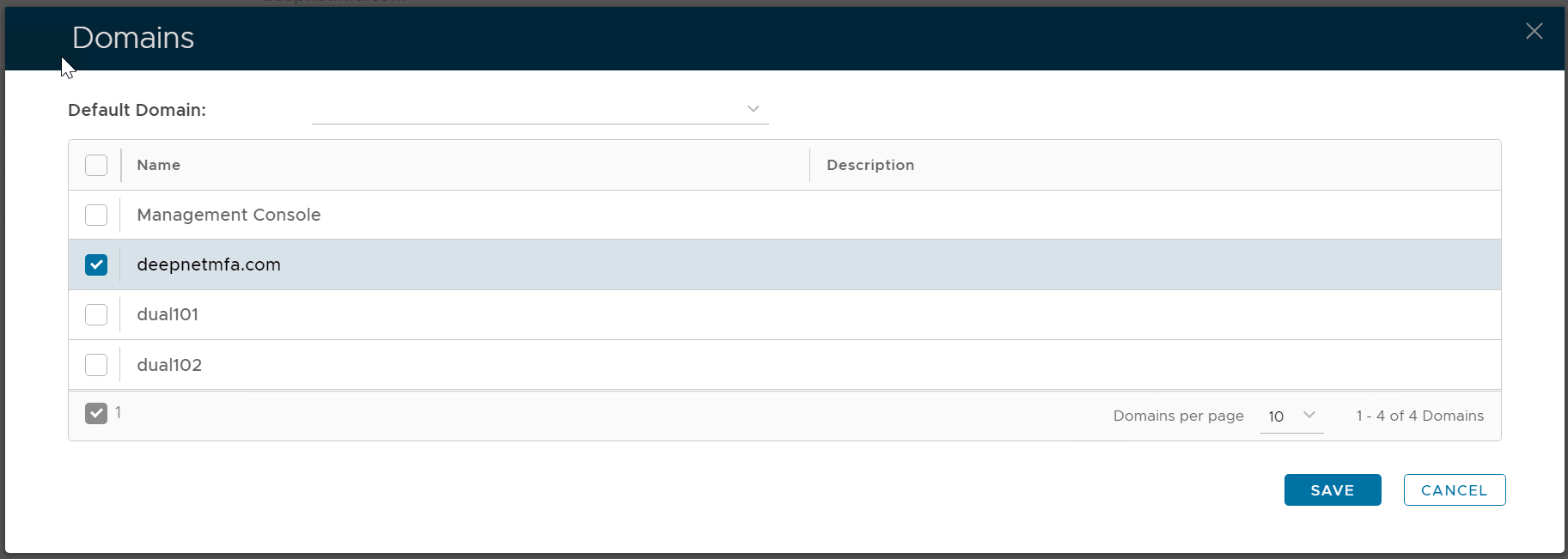
First, you need to add the AD domain into the realm called "Management Console"
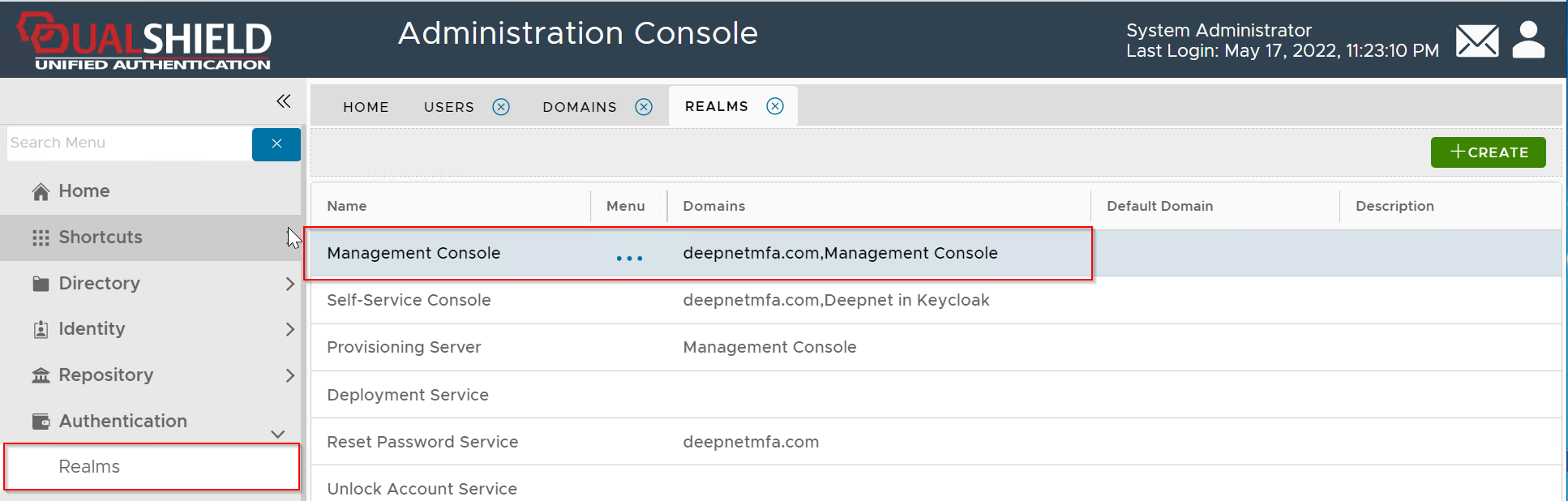
In the example below, the "Management Console" realm includes 2 domains, "deepnetmfa.com" and "Management Console"
"deepnetmfa.com" is an AD domain, which means that users in this domain are allowed to access the Admin Console.
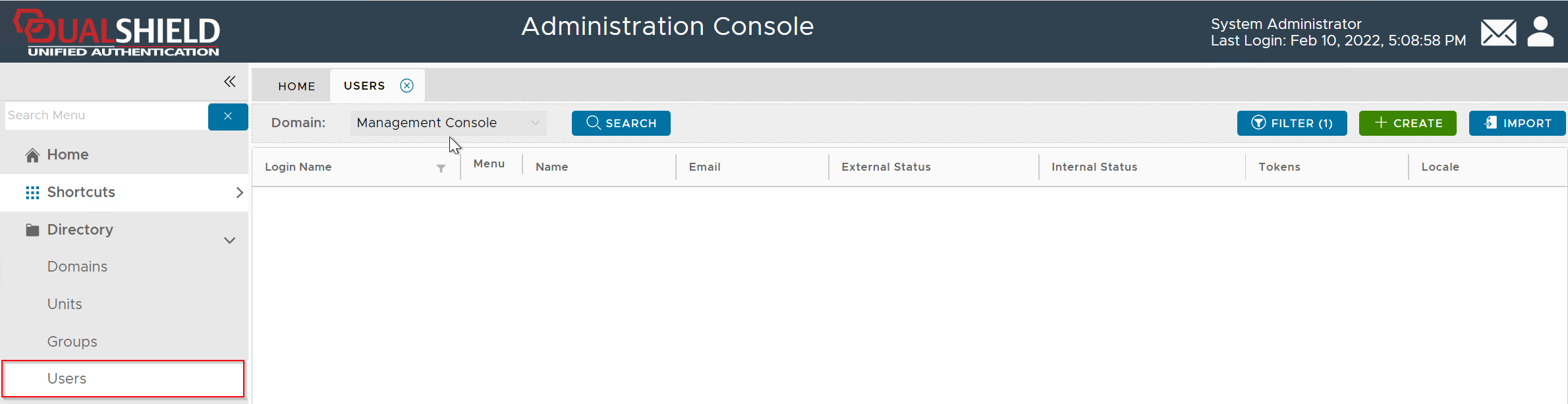
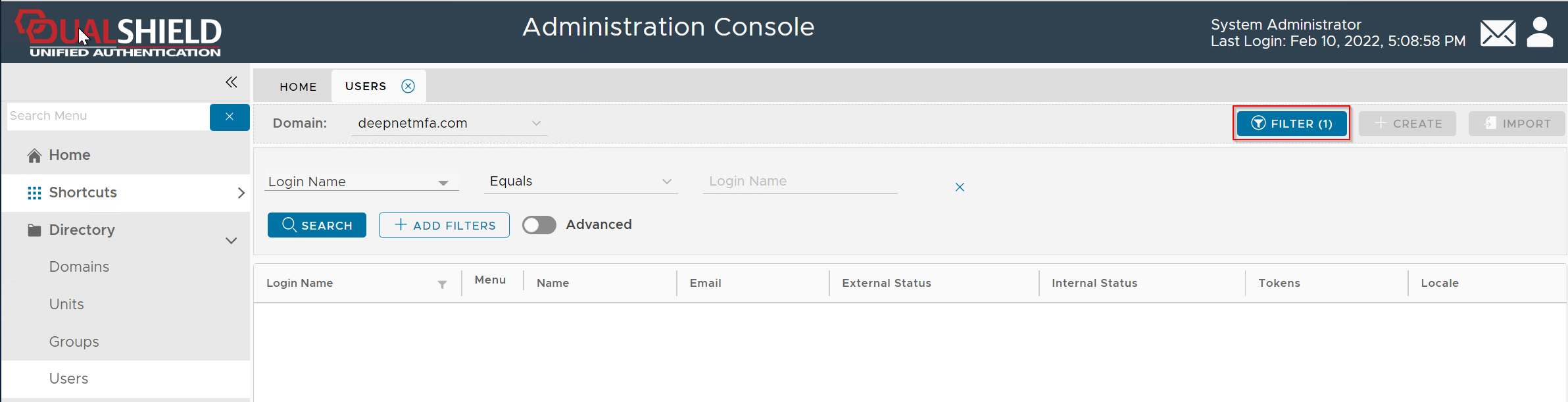
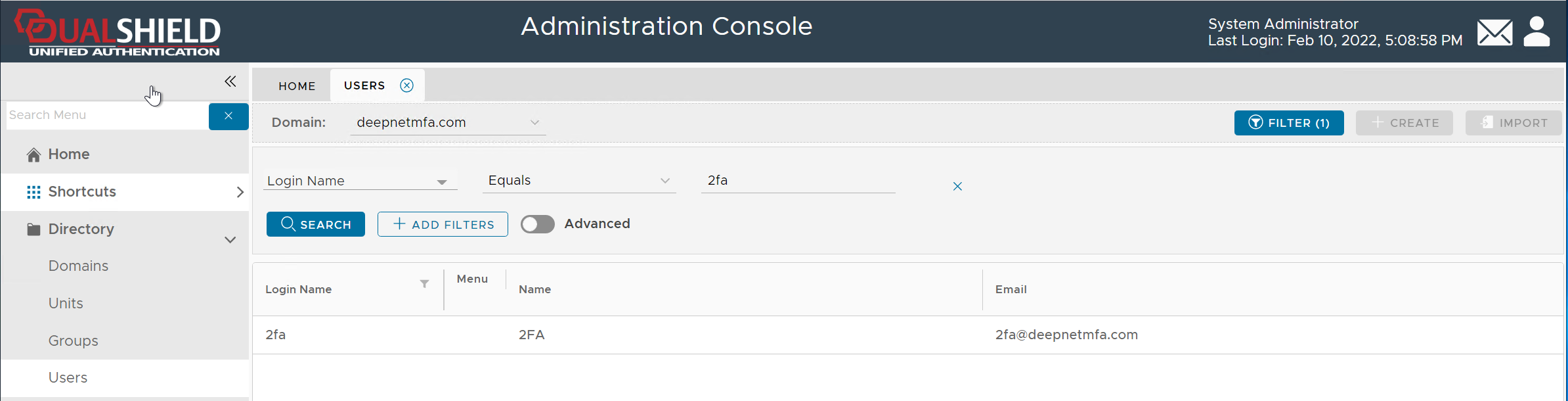
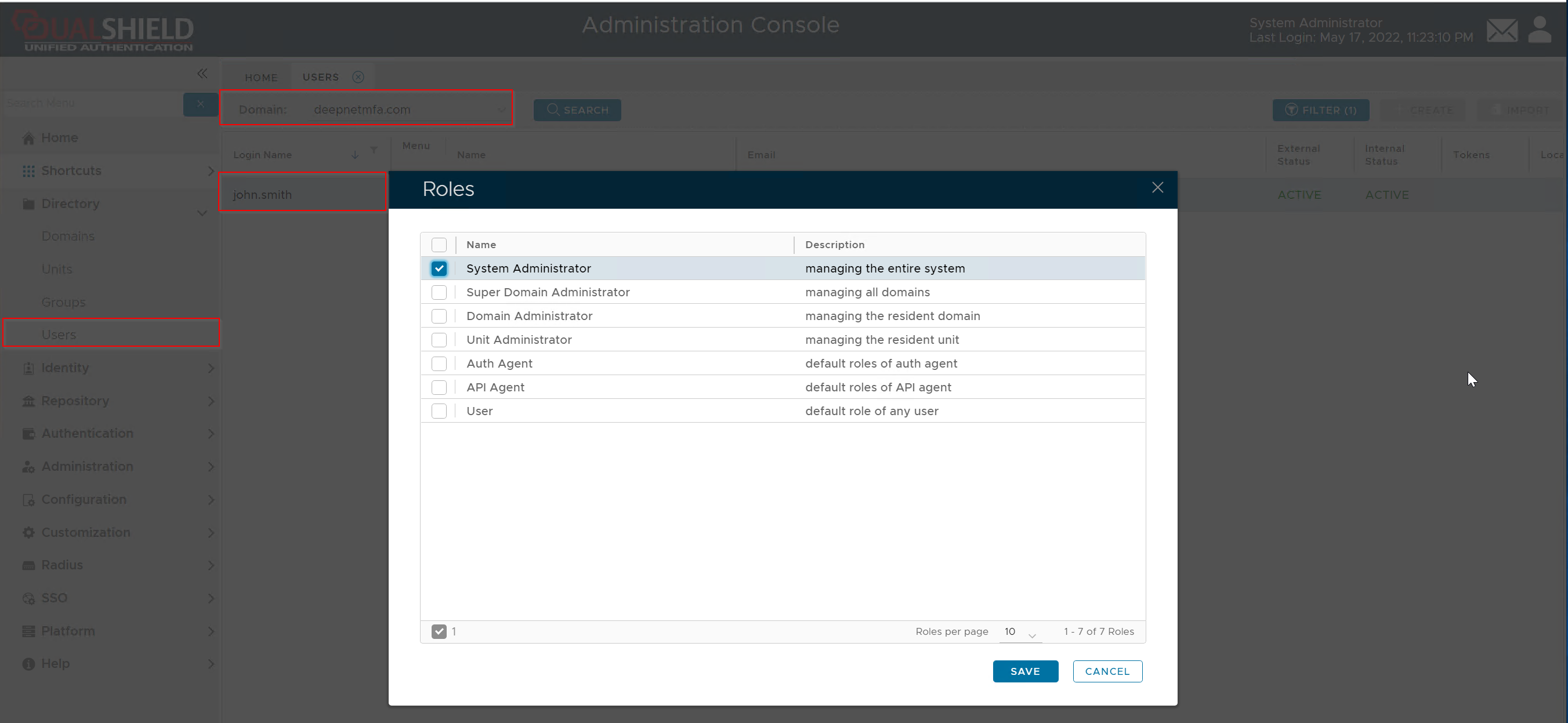
Next, you need to assign an admin or helpdesk role to the users who will authorised to access the Admin Console.
In the example below, a user called "John Smith" in an AD called "deepnetmfa,.com" is being assigned the "System Administrator" role
This means that the AD user "John Smith" will become a System Administrator of the Admin Console.